MAC Flooding: what is this technique that compromises our network

Computer attacks on the network can be very different and have different objectives. Some are designed to steal information and passwords, others infect the system to cause a malfunction, sometimes spy on us … This means that we must always take precautions to protect ourselves adequately. In this article we are going to talk about what MAC Flooding is, one of the many attacks that we can suffer.
What does MAC Flooding mean
As we know, each of the devices that we use to connect to the network has a different MAC address. This is necessary to be able to be identified by the router and, ultimately, to be able to connect and surf the Internet. It is, so to speak, like an identifier. In total there are six blocks of two hexadecimal characters. It is also known as a physical address.
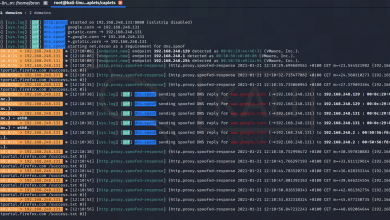
In a network, switches manage MAC address tables. They do this to direct traffic between the different ports in a more efficient way. What an attacker does with this threat is create a flood, a massive request to achieve the collapse of this table that we mentioned.
With this they achieve that, in case of a successful attack, the switch starts to send packets that it receives through all its ports and thus be able to intercept the traffic. This is also known as MAC address saturation.
It must be taken into account that the switch, through these MAC address tables, learns the data dynamically as it manages the traffic. Thus it assigns the different addresses to its different ports through which it reaches the destination. As it is only going to send the data through the corresponding port, it achieves greater efficiency, reducing the network load.
What the attacker does in this case is bombard the switch with a large number of requests, each with a fake MAC address, in order to quickly saturate that table. This means that they will send thousands of fake addresses in seconds.
When this happens, the switch begins to redirect traffic through all ports and allows a sniffer to be used to capture the traffic. This, as we see, puts privacy and security at risk.
Keep in mind that the maximum size of the MAC address table may vary depending on the switch we are using.
How to avoid MAC Flooding attacks
It is important that we always take steps to protect our equipment. Luckily we have tools and functions with which we can prevent the entry of intruders and suffer attacks that put our systems at risk. Privacy and security are very important factors and must always be safe. We must know that these functions are not available in all network switches, but they are available in those that are generally used in companies.
Port limitation
One of these characteristics is to limit the amount of MAC addresses that it will be able to learn on each port. In this way, once it reaches the maximum, it discards all those that are unknown. This prevents the MAC Flooding attack that we have explained.
Static MAC address assignment
We can also choose to configure the switch to assign only MAC addresses statically. This allows us that only packets from certain MACs can be processed.
Disable ports that we do not use
There is also no better security barrier than disabling those ports that we are not using. In this way a possible attacker could not find a way to flood them and thus obtain information.
Avoid connections from other devices
Another option we have to improve security and thus avoid MAC address saturation problems is to prevent it from accepting new connections from other devices.
Ultimately, as we see, MAC Flooding attacks can damage the security of our network switches. It is important that we always take steps to prevent problems that end up affecting the entire network. We have seen some basic tips that we can take into account to prevent attacks.